On Thursday, buzzy sneaker buyers and streetwear aficionados received an email from StockX alerting them to the need to change their password on the popular online marketplace. The Detroit-based company, which was valued at $1 billion in June, pointed to “recently completed system updates on the StockX platform” as the reason behind the seemingly random need for the password changes. But then, something else happened: faced with questions from journalists, StockX revealed there was more going on than a merely routine system update.
Later in the day on Thursday, a StockX spokesman released a statement after being probed by Engadget and revealed that it had “recently [been] alerted to suspicious activity potentially involving our platform,” which is what prompted the company to complete the system updates. “Out of an abundance of caution, we implemented a security update and proactively asked our community to update their account passwords.”
But that was the extent of the information provided. When TechCrunch followed up to inquire about “who alerted StockX to the suspicious activity, if any customer data was compromised and why it misrepresented the reason for the password reset,” the publication stated that StockX declined to provide any further information, thereby, rising questions about the incident, including what – exactly – a company’s duty is to its account holders if data breach has occurred.
The answer is less than straightforward, as in lieu of federal data breach notification laws, it varies on a state-by-state basis. However, there are a few constants in the data hack equation.
For instance, all 50 states maintain legislation requiring private entities to notify individuals of security breaches of information involving personally identifiable information, and according to the National Conference of State Legislatures, the majority of those security breach laws have provisions that “define ‘personal information’ (e.g., name combined with SSN, driver’s license or state ID, account numbers, etc.); what constitutes a breach (e.g., unauthorized acquisition of data); requirements for notice (e.g., timing or method of notice, who must be notified); and exemptions (e.g., for encrypted information).”
The law in Michigan, where StockX is headquartered, for example, defines “security breach” as “the unauthorized access and acquisition of data that compromises the security or confidentiality of personal information maintained … as part of a database.” It goes on to define “personal information” as a “first name or first initial and last name linked to: a social security number, driver license number, state personal identification card number, [and/or] financial account number or credit card or debit card number.”
In accordance with Michigan’s Identity Theft Protection Act, if a company determines that it has suffered from a security breach and that such a breach is “likely to cause substantial loss or injury to, or result in identity theft,” the company is required to “provide a notice of the security breach to each resident of this state whose: unencrypted and unredacted personal information was accessed and acquired by an unauthorized person, and/or personal information was accessed and acquired in encrypted form by a person with unauthorized access to the encryption key.”
As for what companies generally need to disclose to their users and when, Michigan state law says that “without unreasonable delay,” a company should provide notice to consumers in a “clear and conspicuous manner,” describing “the security breach in general terms,” and “the type of personal information that is the subject of the unauthorized access or use,” among other things.
The timing element can be a tricky one, though. This is because legislators, consumers and companies tend to have differing definitions of what is an “unreasonable” amount of time. More than that, “A breach investigation could take weeks or months before you know enough to have a legal obligation to disclose,” Joseph DeMarco, a former head of the cybercrime unit at the U.S. Attorney’s office in Manhattan, told Reuters.
Despite such a lack of uniformly-crafted bright line rules, timing is, nonetheless, one of the primary things that law enforcement looks at in connection with a data hack. Speaking about the sweeping breach of Target’s systems in 2014, a spokesman for the Connecticut Attorney General, for example, said that key issues in determining liability for a company in such matters include “the timeliness and adequacy of notification to appropriate government authorities and to consumers.”
In terms of StockX, the glaring issue at play seems to be tied more closely to its choice of wording – i.e., its conflicting simple “system updates” vs. potential “suspicious activity” explanations – than its timing, since it is unclear when (or even if) the reported breach had taken place. As Jake Williams, founder of Rendition Infosec, told TechCrunch, it was “bad communication” on the part of the burgeoning resale marketplace to initially pass off the situation as a vague “systems update,” only to reveal shortly thereafter that its system may have been compromised and a ton of consumer data right along with it.
It will be interesting to see if StockX’s “bad communication” will have legal ramifications for the resale unicorn, especially since at least some states have enacted private rights of action that enable individuals whose data has been stolen – if that is what happened here – to take action and recover damages, while others’ unfair trade practices statutes “may provide an alternative route to recovery,” according to Pomerantz Law’s Perry Gattegno. (And still yet, the GDPR has stringent rules of its own when it comes to data breach notifications).
More than the legality at play, “Holders of confidential data must weigh the public relations nightmare that often accompanies data breaches, which are becoming high profile, high-stakes messes requiring immediate clean-up,” per Gattegno. “Failing to comply with the relevant statutes not only creates liability, it also causes embarrassment and discourages individuals from entrusting their data to the guilty party.”
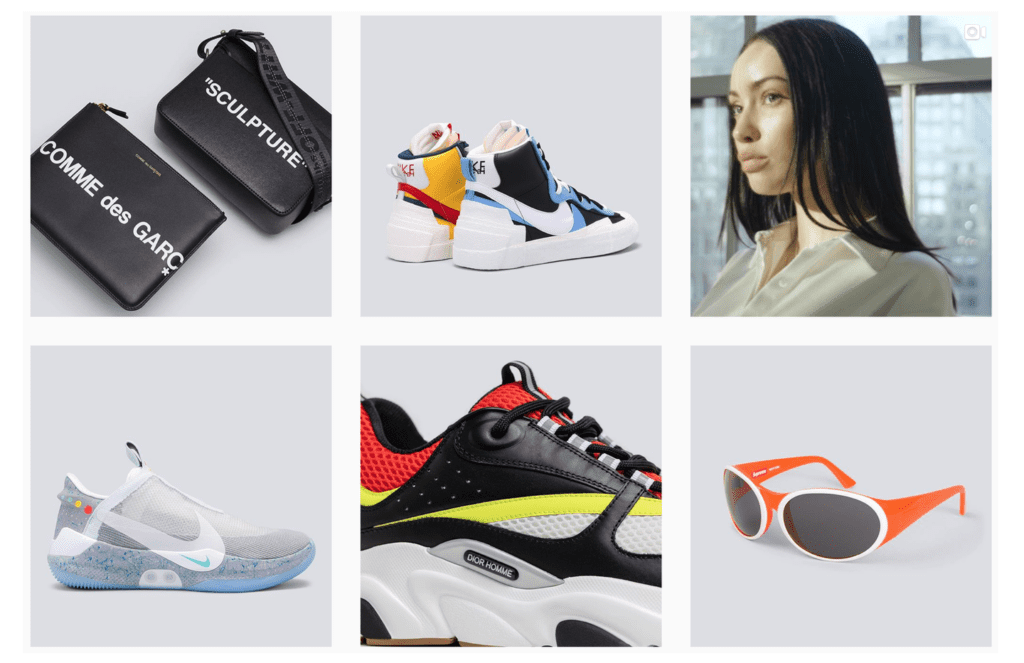
As for consumers, social media comments show that a small number of StockX users are, in fact, put off by the company’s mixed messaging, with some saying that they are swearing off the site altogether. However, a markedly greater number of company’s users appear to be far more bothered by the unsteady service on the company’s site in light of an influx of traffic thanks to a recent restock of Yeezy sneakers. That certainly bodes far better for its public persona than the potential of a sweeping data breach.
A spokesman for StockX says the company is “continuing to investigate,” and noted that “the privacy of our StockX customers is of paramount importance to us.”
UPDATED (August 3, 2019): StockX has confirmed the breach. In a statement provided to Engadget’s Edgar Alvarez, a rep for the company confirmed that “an unknown third party was able to gain access to certain customer data, including customer name, email address, shipping address, username, hashed passwords, and purchase history.” The company further stated, “From our investigation to date, there is no evidence to suggest that customer financial or payment information has been impacted.”
TechCrunch stated on Friday that according to an unnamed source, “More than 6.8 million records were, in fact, stolen from the [StockX site] in May by a hacker,” and are expected to be sold on the “dark web” in due time.
While compromised user names and email addresses may not be enough to give rise to “personal information” in accordance with Michigan’s Identity Theft Protection Act, it may be enough to give rise to liability in other states, such as New York.
New York’s General Business Law defines a “breach of the security of the system” to mean the “unauthorized acquisition or acquisition without valid authorization of computerized data that compromises the security, confidentiality, or integrity of personal information maintained by a business,” with “personal information” includes “any information concerning a natural person which, because of name, number, personal mark, or other identifier, can be used to identify such natural person.”
Significantly, the GDRP maintains a notably low bar when defining “personal data,” and thus, determining what constitutes an actionable breach that requires notification action on the part of the company.
The EU law on data protection – which applies to American companies that “have a presence in an EU country” or “do not have a presence in the EU, but process personal data of European Union residents” – considers personal data to be “any information relating to an identified or identifiable natural person (‘data subject’); an identifiable natural person is one who can be identified, directly or indirectly, in particular by reference to an identifier such as a name, an identification number, location data, an online identifier or to one or more factors specific to the physical, physiological, genetic, mental, economic, cultural or social identity of that natural person.”
The GDPR requires that companies report certain types of personal data breach to the relevant supervisory authority within 72 hours of becoming aware of the breach. If the breach is not reported within this time frame, the company must provide reasons for the delay.
As TechCrunch aptly notes, in accordance with the GDRP, a company can be fined up to four percent of its global annual revenue if found to be in violation of the sweeping privacy law.
It is unclear if StockX has alerted European users to the reported breach and/or required that they update their passwords. An unnamed StockX user, who is based in the UK, told TFL on Friday that he was not contacted by StockX about the “system updates” nor was he prompted to change his password.